Apple has introduced the invention of a severe safety vulnerability for iPhones, iPads and Macs which may probably permit attackers to take full management of a sufferer’s gadgets.
Fortunately the announcement got here as Apple launched a safety replace that may forestall the assault from happening.
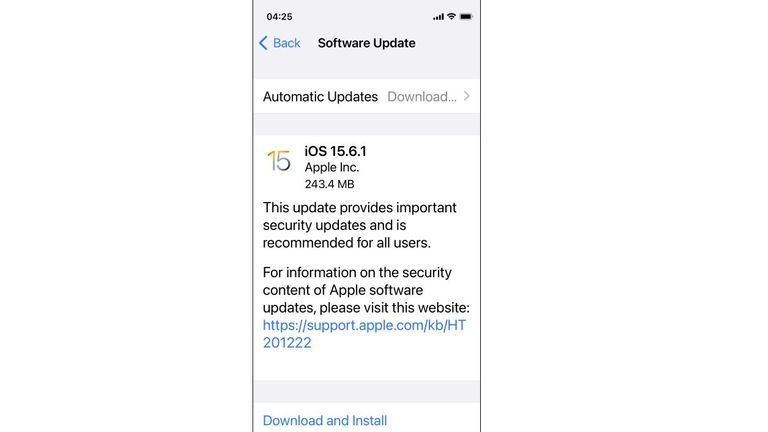
To set up this safety replace, you’ll be able to go to the Settings App, then General, then Software Updates.
The newest model of iOS and iPadOS is 15.6.1, whereas macOS is on 12.5.1.
How did the assault work?
According to Apple the vulnerability may have been exploited by “processing web content”, that means accessing an online web page which contained malicious code.
Any attackers that knew in regards to the vulnerability – and find out how to exploit it – may, by directing a sufferer to such an online web page, have the ability to execute any code they needed on the sufferer’s system.
Usually gadgets limit the sorts of code that may be run on them to customers with explicit ranges of privileges – however this vulnerability allowed the code to be executed with kernel privilege.
The kernel is the core a part of iOS. It has unrestricted entry to all points of the working system – that means the attacker may have full management over the sufferer’s system.
Who was utilizing it to assault folks?
Apple mentioned it’s conscious of a report that the vulnerability could have been actively exploited.
However the corporate didn’t supply any further particulars.
What is the chance to most people?
Within the cyber safety world, the flexibility to execute code on a sufferer’s system simply by making them open an online web page is extraordinarily uncommon and highly effective.
As a easy matter of provide and demand, the exploit may have been bought for some huge cash – and in that case, then it will seemingly have been used to assault a high-value goal.
Offensive cyber instruments like exploits for severe vulnerabilities like this do not final ceaselessly.
As quickly because the vulnerability is found then the software program vendor can start creating a repair for it – and any try to use the vulnerability dangers revealing that it exists.
This restricted time during which a vulnerability could be exploited additionally impacts the market dynamics for promoting, buying and utilizing such instruments.
All of because of this earlier than the vulnerability was found by Apple – when it was a “zero day” vulnerability as a result of the seller had zero days to develop the patch – it will seemingly not be used for normal concentrating on.
However now that the vulnerability is publicly recognized, it might be that criminals reverse engineer the safety replace and goal members of the general public who have not but up to date their gadgets.
This is why it’s so necessary to put in the most recent safety updates.
Who discovered this difficulty?
The researcher who reported the vulnerability selected to stay nameless.
There might be quite a lot of causes for them doing so, together with merely that they did not need the eye that the report would have introduced them.
Potentially it is also that the researcher works for an organization or authorities organisation that was focused by way of this vulnerability.
If so, revealing that they knew in regards to the assault – by attributing the disclosure to a reputation related to the sufferer – may present the attacker with some suggestions about their offensive operation.
Read extra: GCHQ reveals why it retains some software program vulnerabilities secret
Alternatively, it might be that the vulnerability was reported by a Western authorities with a vulnerabilities fairness course of, such because the UK’s National Cyber Security Centre, part of GCHQ.
It could have been that the safety and intelligence companies had a necessity to use the vulnerability, however having carried out so selected to reveal it to Apple in order that it might be mounted.
There isn’t any proof for any of the above situations, they’re offered as some examples of the totally different causes the researcher could have chosen to stay nameless.
Source: information.sky.com”